Webinar
Donu’t Let Vulnerabilities Create a Hole in Your Organization
Open source code is everywhere, and for good reason – it helps developers deliver code quickly and efficiently. If those open source components are insecure, it could result in a catastrophic data breach. So, how do organizations prevent this from happening?
View the Webinar
What will you learn?
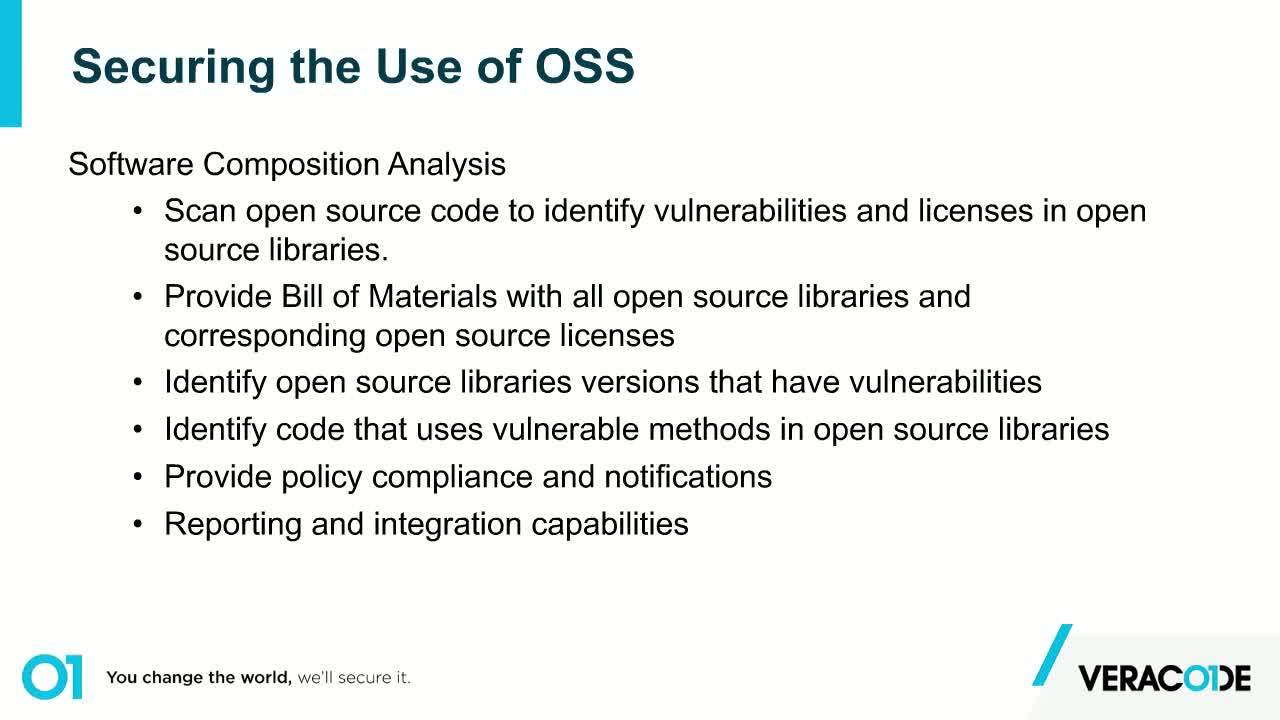
Software Composition Analysis (SCA) is helping companies identify vulnerabilities in the open source libraries they’re using. Watch this webinar to learn how Veracode SCA can:
• Help your development teams easily identify which open source libraries are in use
• Protect your applications and customer data
Speaker: Javier Perez, Director, Product Management, Veracode
Original Air Date: Wednesday, October 2, 2019